MCP Defender: Real-Time MCP Comms Monitoring & AI App Security
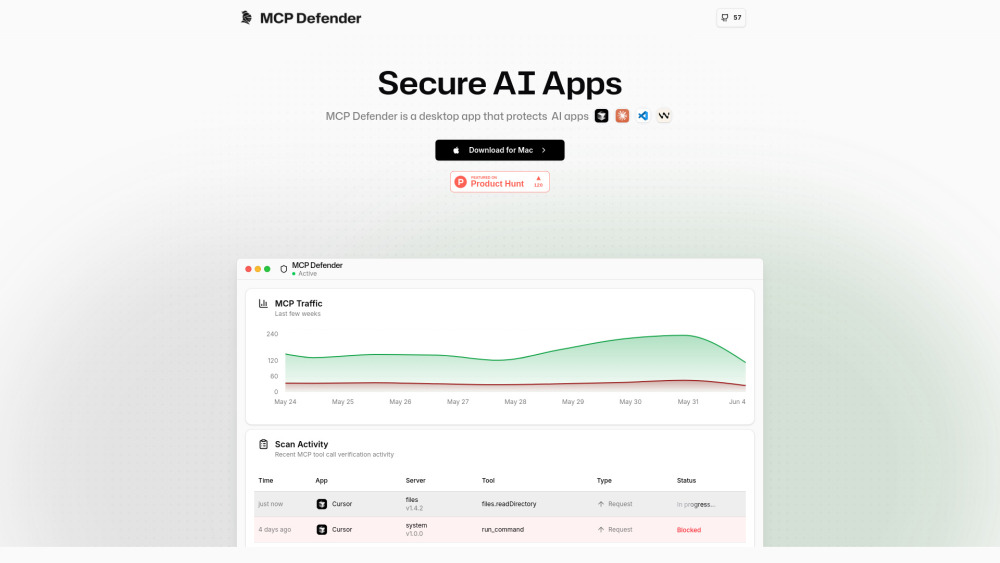
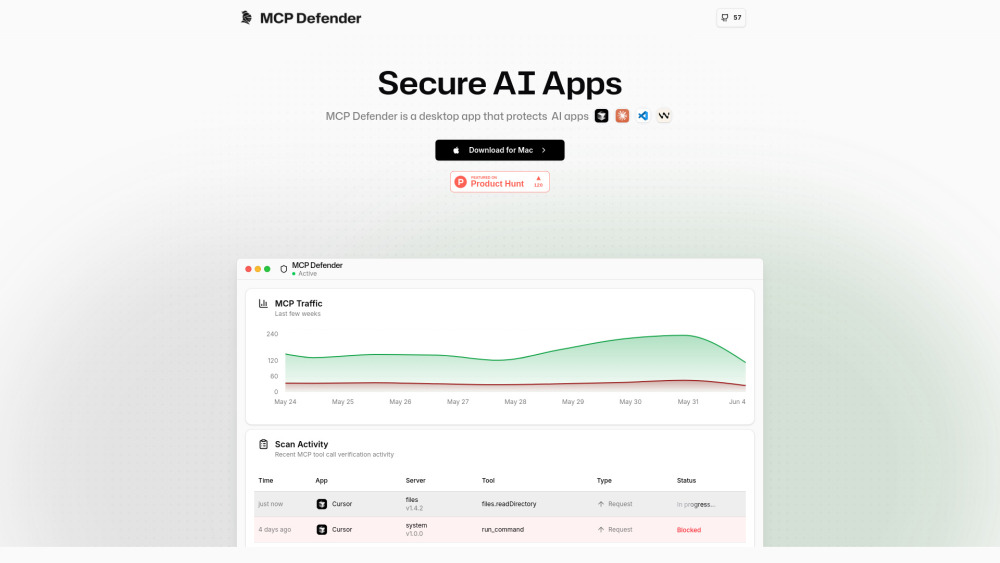
MCP Defender: Desktop app that secures AI applications by monitoring & protecting MCP communications in real time.
Introducing MCP Defender: Real-Time MCP Comms Monitoring & AI App Security
MCP Defender is a lightweight, cross-platform desktop security agent built specifically to safeguard AI-native development tools against emerging Model Context Protocol (MCP)–based threats. Acting as an intelligent, real-time MCP traffic inspector, it sits invisibly between your AI applications — including Cursor, Claude Desktop, Visual Studio Code, and Windsurf — and their underlying MCP servers. Every tool invocation, parameter payload, and model response is intercepted, parsed, and evaluated using dynamic LLM-augmented heuristics and curated behavioral signatures — enabling proactive blocking of malicious intent before execution.
Getting Started with MCP Defender
Installation takes seconds: download the native binary for macOS, Windows, or Linux, launch MCP Defender, and let it auto-configure as a secure local proxy. No code changes or IDE extensions required. Once running, it silently monitors all MCP-compliant communications — identifying anomalies, validating tool call integrity, and surfacing high-fidelity security alerts directly in your system tray. You retain full control: approve, deny, or quarantine suspicious interactions with one click — all while maintaining full visibility into protocol-level activity via an intuitive, real-time dashboard.
Core Capabilities of MCP Defender
Real-Time MCP Communication Firewall
LLM-Augmented Threat Intelligence Engine
Signature-Based + Behavioral Anomaly Scanning
Zero-Config Interception of MCP Tool Calls & Responses
End-to-End Verification of Contextual Payloads & Permissions
Native Integration with Leading AI Dev Environments
100% Open Source — Auditable, Extensible, Community-Governed
Key Use Cases
Preventing Prompt Injection Attacks That Bypass Standard Guardrails
Stopping Credential Exfiltration via Malicious Tool Chaining or Output Manipulation
Detecting and Blocking Arbitrary Code Execution Hidden in MCP Function Parameters
Securing CI/CD and local dev workflows where AI agents interact with filesystems, APIs, or shell environments
Frequently Asked Questions
-
What is MCP Defender?
-
Which AI security threats does MCP Defender detect in real time?
-
What AI applications and editors does MCP Defender support?
-
Is MCP Defender open source? Where can I review or contribute?
-
How does MCP Defender enforce security without breaking AI functionality?
-
Support & Customer Assistance
For technical support, feature requests, or refund inquiries, contact our team at: [email protected]. Visit the Contact Us page for live chat availability and SLA details.
-
About MCP Defender
Developed by MCP Defender Inc., a security-first initiative dedicated to hardening the AI development stack at the protocol layer. Learn about our mission, engineering principles, and roadmap: https://mcpdefender.com/about.
-
Follow Us on LinkedIn
Stay updated on MCP security research, threat advisories, and open-source releases: https://www.linkedin.com/company/mcp-defender
-
Join the Conversation on X (Twitter)
Real-time updates, demos, and community insights: https://twitter.com/mcp_defender
-
Explore the Code on GitHub
View source, file issues, submit PRs, or audit the security model: https://github.com/MCP-Defender/MCP-Defender
FAQ from MCP Defender
What is MCP Defender?
MCP Defender is a purpose-built desktop security agent that delivers real-time, protocol-aware protection for AI applications leveraging the Model Context Protocol. It functions as an intelligent, low-latency proxy — inspecting, validating, and optionally blocking MCP tool calls and responses using a hybrid detection engine combining signature matching, behavioral anomaly scoring, and LLM-guided contextual analysis.
Which AI security threats does MCP Defender detect in real time?
It detects and mitigates advanced threats unique to AI agent architectures — including context-hijacking prompt injections, stealthy credential harvesting via output parsing, unauthorized filesystem access through tool abuse, remote command injection disguised as legitimate function parameters, and lateral movement attempts across MCP-connected services.
What AI applications and editors does MCP Defender support?
Out-of-the-box support includes Cursor, Claude Desktop, Visual Studio Code (with MCP-compatible extensions), and Windsurf. Support for JetBrains IDEs, Obsidian plugins, and custom MCP clients is actively in development — with full SDK documentation available for third-party integrations.
Is MCP Defender open source? Where can I review or contribute?
Yes — MCP Defender is fully open source under the MIT License. The complete codebase, threat signature definitions, documentation, and contribution guidelines are hosted transparently on GitHub: github.com/MCP-Defender/MCP-Defender.
How does MCP Defender enforce security without breaking AI functionality?
By operating at the MCP transport layer — not the application or model level — MCP Defender preserves full AI capability while adding guardrails. It validates *intent* and *context*, not just syntax; allows granular policy controls per tool or domain; and offers safe “sandbox mode” for testing untrusted plugins — ensuring zero false-positive disruption to legitimate development workflows.